
Your most critical credentials are often the easiest path for a cyber attacker to exploit. When passwords, tokens, and other digital secrets leak, traditional security defenses are bypassed instantly. To understand why robust, sustainable secrets management is essential, we first need to understand what secrets are and why certain practices for keeping them safe are no longer sufficient.
Everyone – from early-stage startups to large enterprises, open source projects, and heavily regulated industries – relies on secrets. API tokens, private keys, database credentials, cloud access keys, and signing keys are all examples of secrets. Modern systems simply can't function without them.
When these critical pieces leak – because they are stored insecurely, shared too widely, rarely rotated, or left unaudited – attackers gain instant access. A stolen secret allows them to impersonate trusted users, services, or systems without triggering traditional exploit paths.
Secrets management reduces this risk. It securely stores secrets, controls and audits access, delivers them safely to workloads, and manages their lifecycle through rotation and revocation. This shrinks unauthorized access, limits credential-based attacks, and prevents long-lived misuse. As systems scale, robust secrets management solutions like OpenBao become an essential component of operational infrastructure.
A secret is any confidential information that exists to protect infrastructure, applications, and services from unauthenticated and unauthorized access. They act as authentication credentials between users, systems, and components, ensuring that only trusted identities can access sensitive resources such as databases, cloud APIs, internal services, etc. In modern distributed systems, secrets are a primary mechanism for enforcing identity and access control.
Secrets grant access through possession alone. No extra checks are needed. If a secret is valid, access is granted, except where "condition access" evaluates additional factors. This sets secrets apart from many other security mechanisms. A vulnerability typically requires exploitation. With a leaked secret, access is granted by design, because the system cannot distinguish between a legitimate holder and an attacker. This is why secrets are especially dangerous when exposed and therefore require tight control implemented through secrets management solutions.
Both people and applications use secrets, but scale, speed, and risk profiles differ sharply. Distinguishing between them is important, because they require different management approaches.
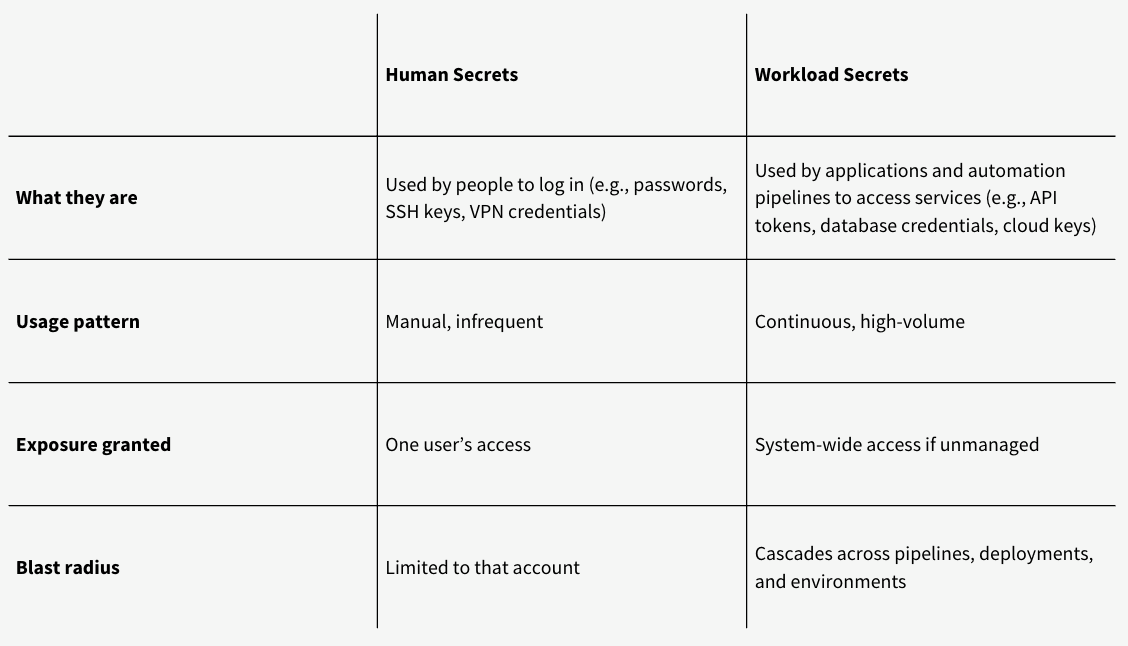
Workload secrets dominate modern risk due to their scope, scale, and speed. When compromised, they allow attackers to act as automation: triggering deployments, pulling or pushing container images, accessing production databases, invoking cloud APIs, and moving laterally between services in seconds. For this reason, discussions of exploitability and blast radius focus primarily on workload secrets.
Password managers like Vaultwarden excel at protecting human secrets – SSH keys, VPN credentials, and team passwords stay secure through autofill and controlled sharing.
Modern infrastructure, however, runs on workload secrets (API tokens, database credentials, cloud keys) that applications need continuously with automation at scale. Password managers are not designed for this use case: they lack runtime APIs for Kubernetes workloads, dynamic credential generation, and automated rotation.
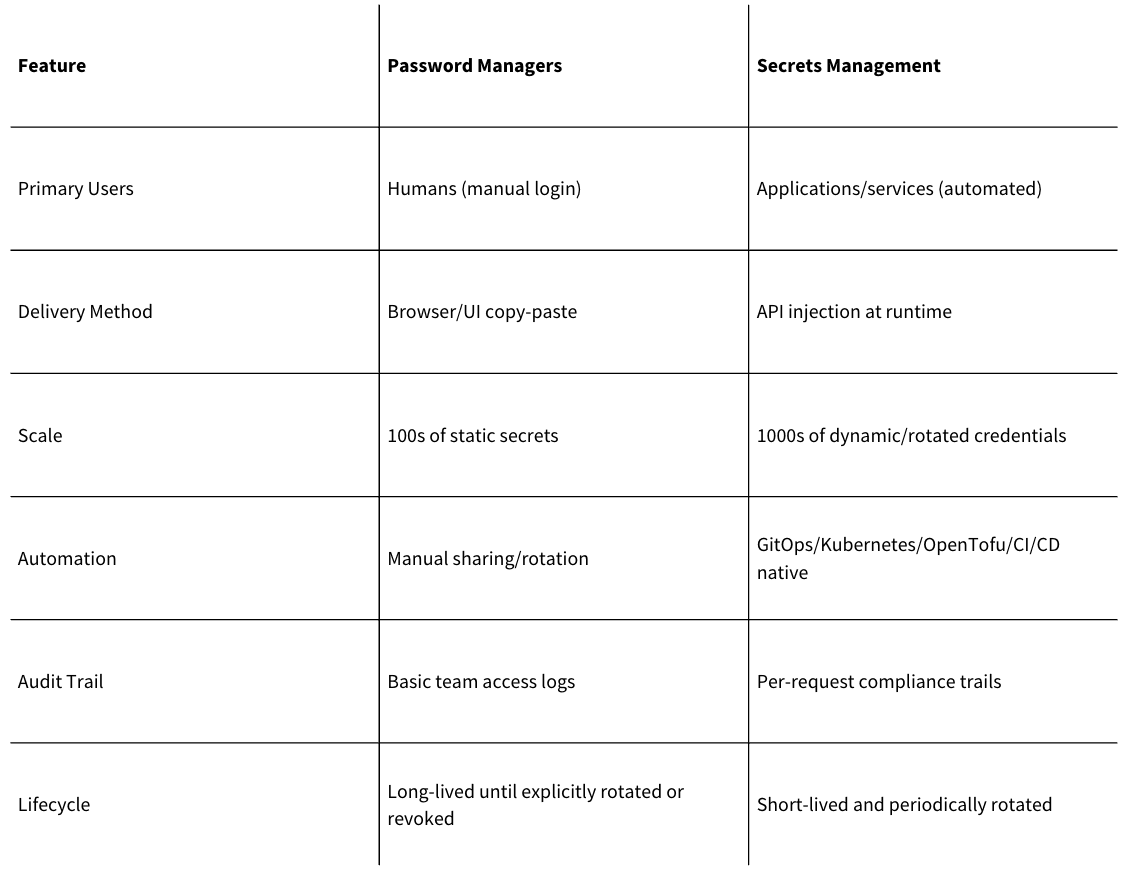
TL;DR: Password managers secure people-to-machine access. Secrets management solutions secure machine-to-machine access. While password managers secure human secrets well, they are not for workload secrets. Workload secrets must be managed with dedicated secrets management.
Secrets, without proper controls, are easy to exploit because of four inherent traits:
These traits become easier to understand in practice with a concrete example.
Example: Consider a CI/CD pipeline that uses AWS access key ID and AWS secret access key to deploy infrastructure to AWS:
If the keys leak through a git repository, build log, or compromised pipeline runner, an attacker gains the same permissions attached to the access keys. No exploit is required. Possession alone is enough. Since the usage of the keys may not be closely monitored, misuse can go unnoticed for a dangerous amount of time.
A single leaked workload secret can cascade into widespread damage. Secrets management reduces this risk by limiting where secrets live, how long they remain valid, and how they are accessed, particularly at workload scale.
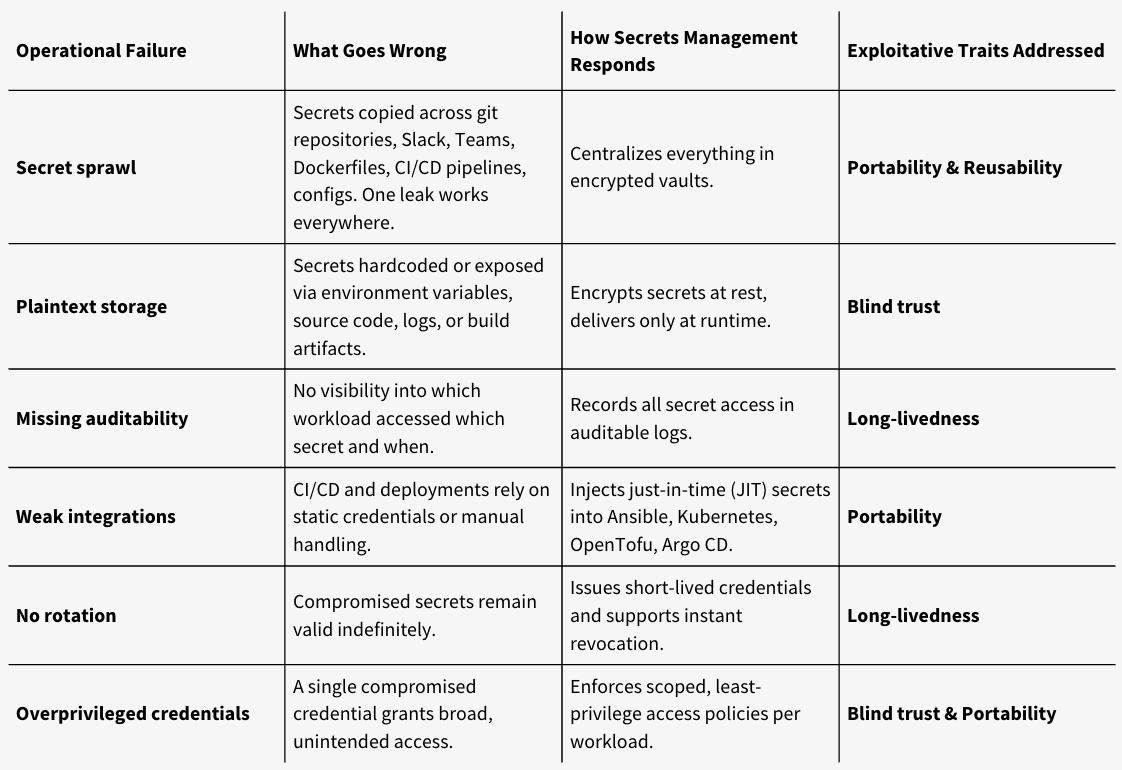
These traits – portability, long-livedness, and blind trust – do not just make secrets exploitable. In real systems, they manifest as recurring operational failures that grow harder to detect and contain as automation increases.
The table below maps common failure modes to the exploitative traits they stem from and the controls secrets management introduces to address them:
As automation and credential sharing increase, ad-hoc approaches introduce friction and risk. Refer to the table below to see what risks may appear in your current stack, and the controls secrets management puts in place to address them:
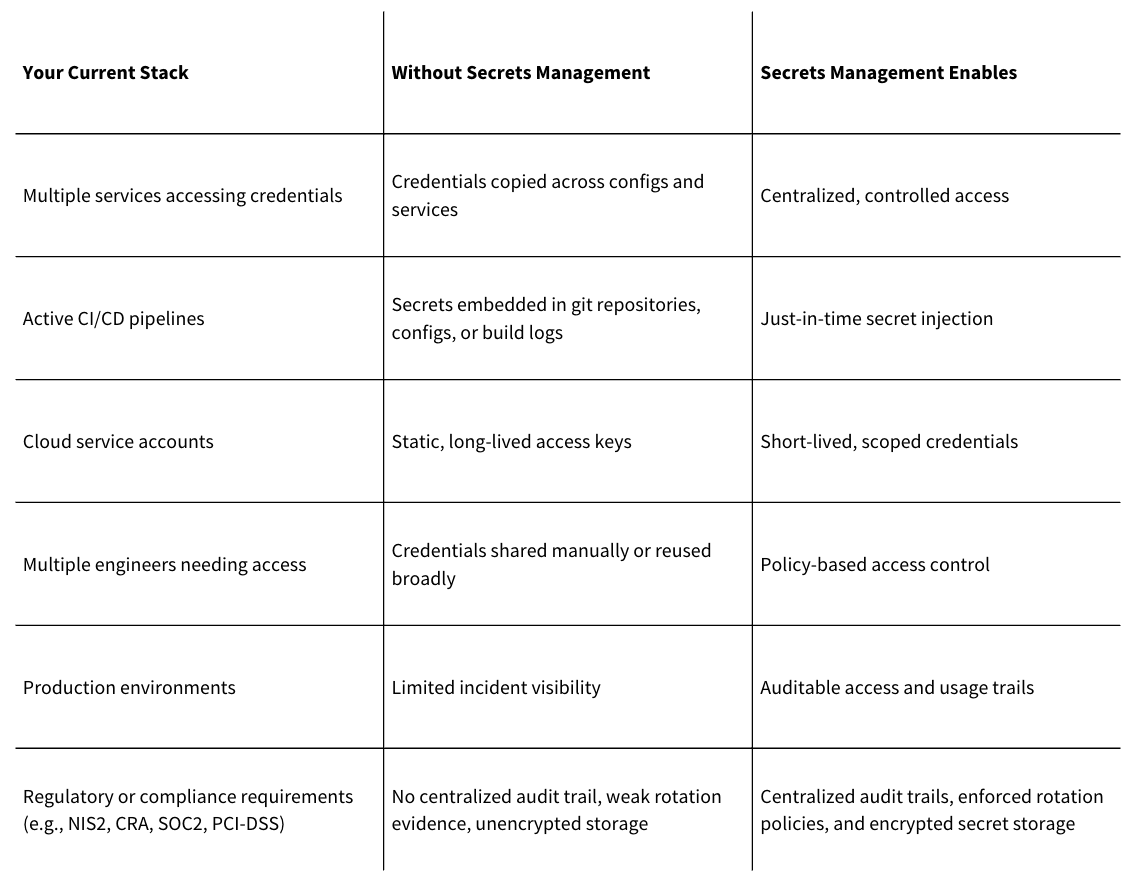
Secrets management becomes necessary when automation outpaces manual control. At that point, managing how workloads authenticate, how long credentials remain valid, and who or what can access them requires centralized policy, auditability, and lifecycle automation.
Secrets management solutions like OpenBao provide these primitives and integrate directly with platforms such as Ansible, Kubernetes, Linux workloads, OpenTofu, and GitOps workflows, allowing infrastructure to scale while maintaining clear control over how workloads authenticate and what systems they can access.
If you are evaluating secrets management for your infrastructure and want guidance grounded in a decade of domain expertise, Adfinis can help. Our discovery workshop provides an objective analysis of your requirements to help you choose the best path – whether that leads to OpenBao or a different strategy.
As a co-maintainer and member of the OpenBao project's Technical Steering Committee (TSC), Adfinis is uniquely positioned to help organizations. We specialize in the secure design, deployment, and operation of OpenBao, serving all organization types, with a focus on enterprise and regulated industries. Furthermore, through our Secretz Enterprise subscription, we deliver 24/7 enterprise support and software assurance for OpenBao.
Reach out to start mapping your secrets management strategy!
Learn more about secrets management from our other blog posts: